Continuous Vigilance in Supply Chain Data Security
There is no higher priority than data security and business continuity when we develop our IT tools, systems and operational processes. ALOM is SOC2 and Privacy Shield certified to ensure global data privacy and information security integral to protecting our customers and their end-users. Our redundant systems and globally integrated facilities ensure continuity and fast recovery from any disruption.
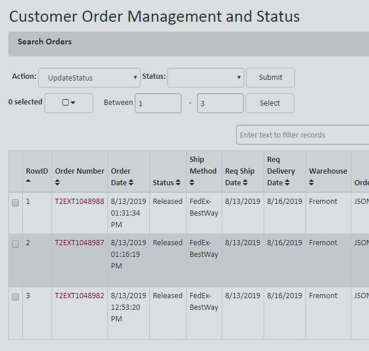

As orders are fulfilled and released for shipment they flow into our MegaShipper database. This sophisticated yet user-friendly system tracks order source, characteristics, shipping date and time authorizations, and monitors delivery status while providing real-time reports.
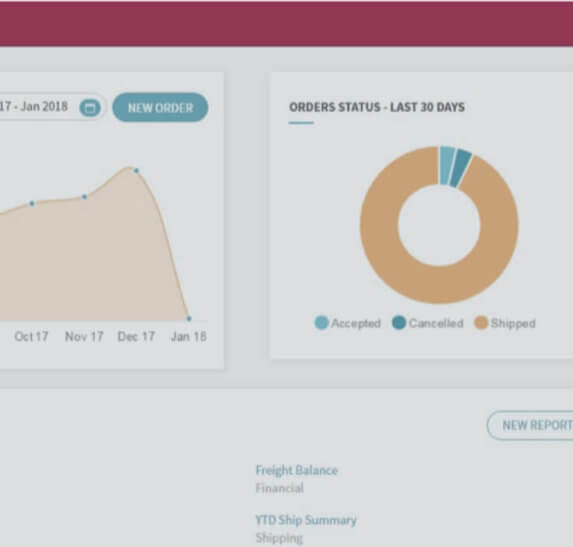

COMPASS™ is our powerful, proprietary order management portal that provides customers and ALOM operations teams with real-time order intake and status visibility. The COMPASS dashboard features customizable views of activity, provides actionable status alerts and detailed report data.


ALOM BI is a business intelligence tool that continuously analyzes current and historical data across the ALOM global network, presenting it on customer dashboards to provide visibility and measure achievement of supply chain objectives.